Blue Team Labs Online - Frontier
Security Operations
Tags: In this Frontier Space Station (FSS) security investigation, we delve into an unsettling incident surrounding Head Paladin Luis Harrold's workstation within our faction's space station.
Scenario In this Frontier Space Station (FSS) security investigation, we delve into an unsettling incident surrounding Head Paladin Luis Harrold's workstation within our faction's space station. Upon his return from rationing lunch supplies, Harrold discovered an image displayed on his terminal. Our mission is to uncover the origins of this mysterious image and evaluate potential security breaches within our network. By employing Potatu Bot image analysis, Potatu Bot access logs scrutiny, and Potatu Bot network traffic analysis, our goal is to pinpoint the source of the image and any clandestine intrusions. Recommendations for bolstering our station's defenses, refining our incident response protocols, and educating fellow nearby stations on security awareness will be disseminated based on our findings.
Environment Awareness
Evidence Discovery
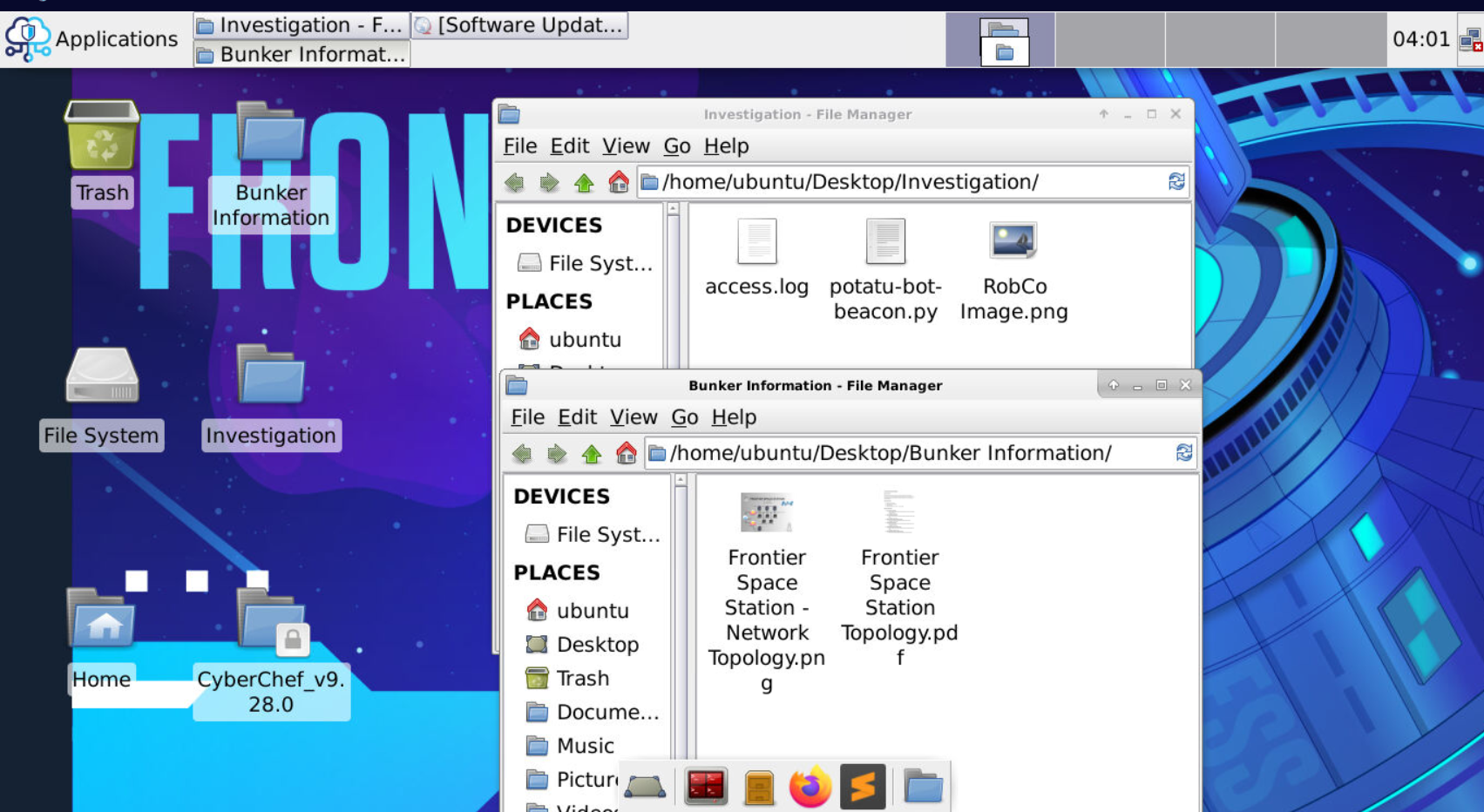
There are 3 directories that will be used on this investigation
- First is Bunker Information that contains network topology of Frontier Space Station that will be used in Q4-5.
- Second is Investigation that contains access.log, python script that will detect HTTP beacon from access.log and lastly an image file that was the culprit of this incident.
- And Lastly, CyberChef which could be used in Q2
Investigation
Q1) Luis Harrold mentioned a strange image on his device. Looking into it further, what is the true “file type” of this image? (Format: FileType)
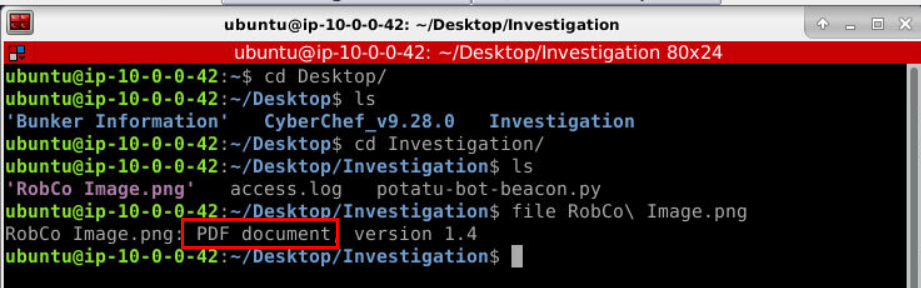
To answer Q1, we need to use file command to an image file provided and turns out its a spoofed PDF document which likely to contains malicious Javascript that will be triggered upon open.
Answer
pdf
Q2) Let’s look for Indicators of Compromise, such as URLs. What are the three suspicious URLs within the file in respective order—defanged? (Format: URL1, URL2, URL3)
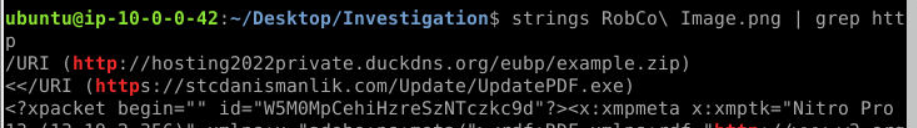
Since most website start with http so I used strings "RobCo Image.png" | grep http to find out which could we use to filter which we could see that from the result of this command, there are /URI tag that we could use to filter all IOC (as URL) from this file
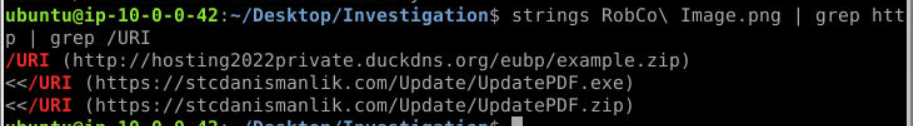
So I did that and we got 3 URLs in respective order but its time to defang them.
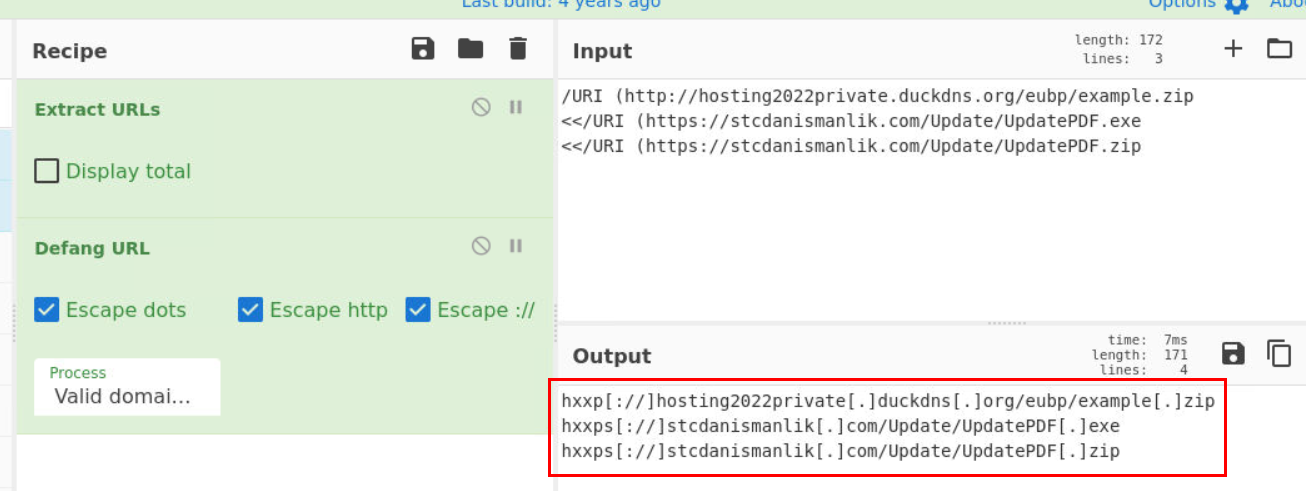
We can easily do this via CyberChef with Defang URL
Answer
hxxp[://]hosting2022private[.]duckdns[.]org/eubp/example[.]zip,hxxps[://]stcdanismanlik[.]com/Update/UpdatePDF[.]exe,hxxps[://]stcdanismanlik[.]com/Update/UpdatePDF[.]zipQ3) We have the right to believe this attack was from that paramilitary organization—those war space criminals known as “enclave”. Where did Luis download the image from? (Format: URL)
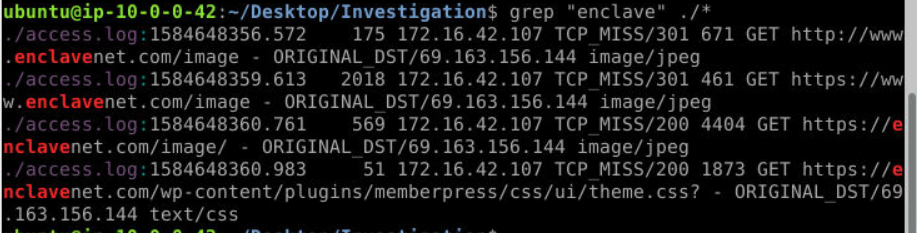 Alright so we can just search for "enclave" with grep on
Alright so we can just search for "enclave" with grep on access.log then we will get criminals' URL that hosted an image.
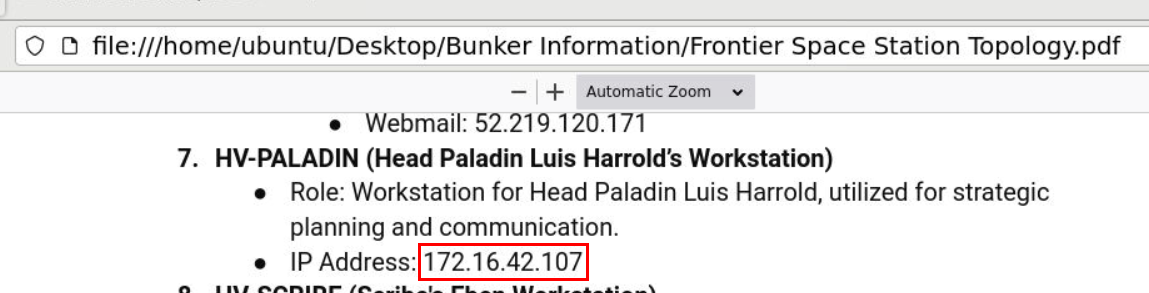 And after confirm with FSS Topology, its confirmed that Luis downloaded the image from this url.
And after confirm with FSS Topology, its confirmed that Luis downloaded the image from this url.
Answer
http://www.enclavenet.com/imageQ4) Suspicious activity is arising from Luis' computer as we dive deeper. Let’s run the Potatu Bot Beacon against the access.log with Luis' IP in mind. Please, look for a minimum of 10 beacons (-c) that are at 5-second intervals (-i). What URL has the highest amount of traffic? (Format: URL)
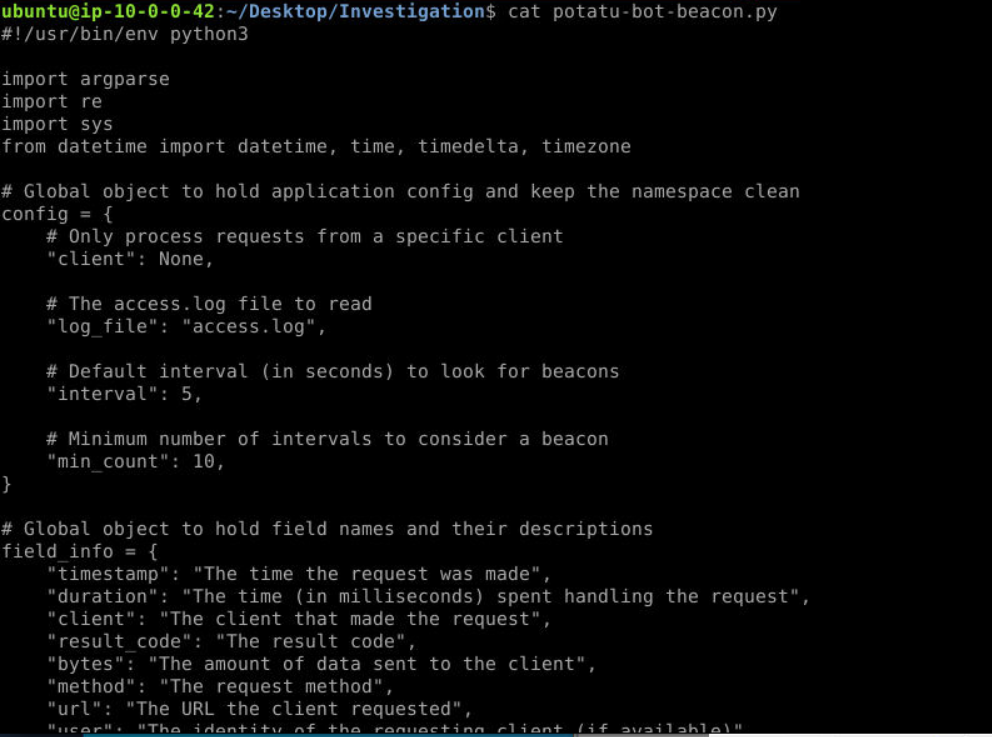 Lets take a look at the script before we run it and as you can see that its parse
Lets take a look at the script before we run it and as you can see that its parse access.log file to each URL then calculated each interval of beaconing to each URL and will only display result based on provided interval (in second) and number of beacon
and as you can see that those default config are already match our need so we could just only provide an IP address and log file.
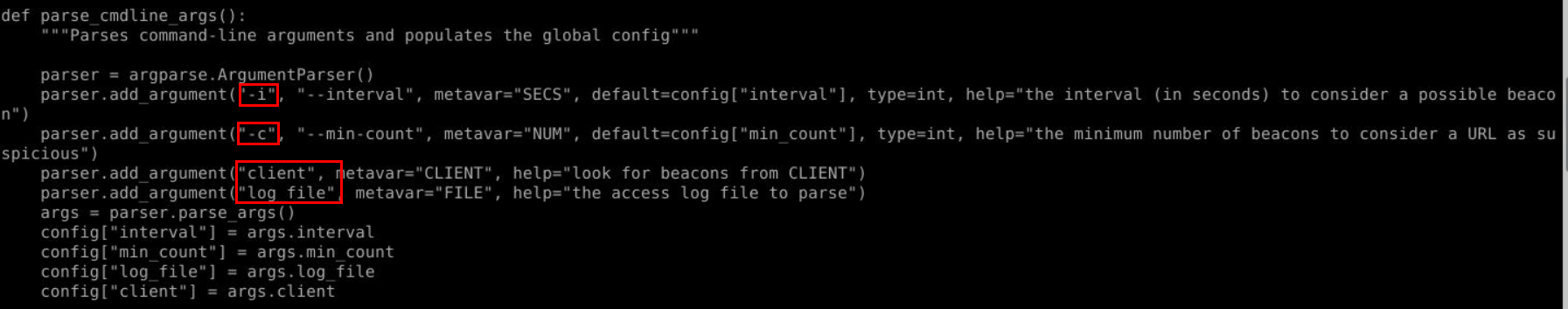
This python script can take 4 arguments at most and will put them to config and I do not want to mess with the order so I will run this script with 4 arguments
 Give it execution permission then execute it with
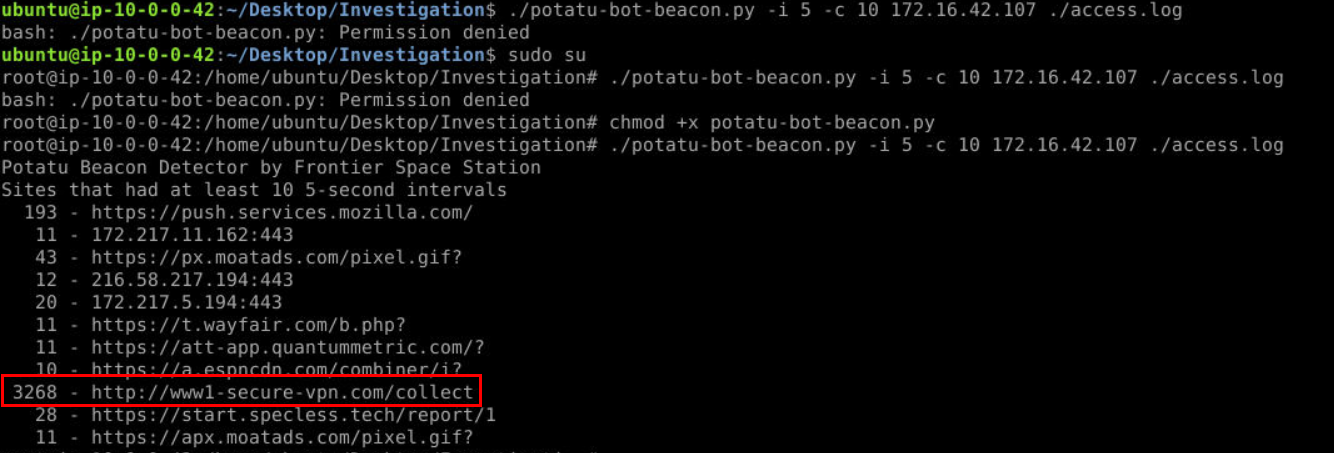
Give it execution permission then execute it with ./potatu-bot-beacon.py -i 5 -c 10 172.16.42.107 ./access.log then we should have the the highest number of beacon right here.
Answer
http://www1-secure-vpn.com/collectQ5) Lastly, let’s find additional hosts in the space station network that are compromised and reach out to the domain above. Place the hostnames in their respective order—including Luis' machine (Format: Host1, Host2, Host3, Host4)
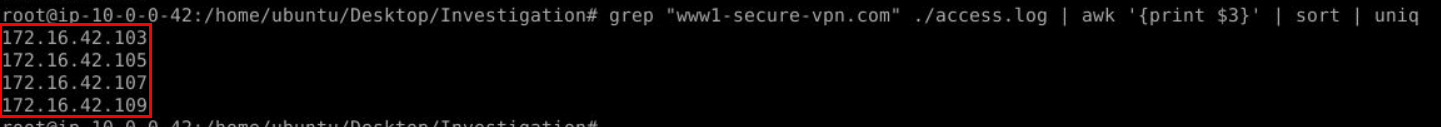
We got the domain so we could just use grep with awk and sort | uniq to filter out unique IP addresses from access.log that beaconing to this domain.
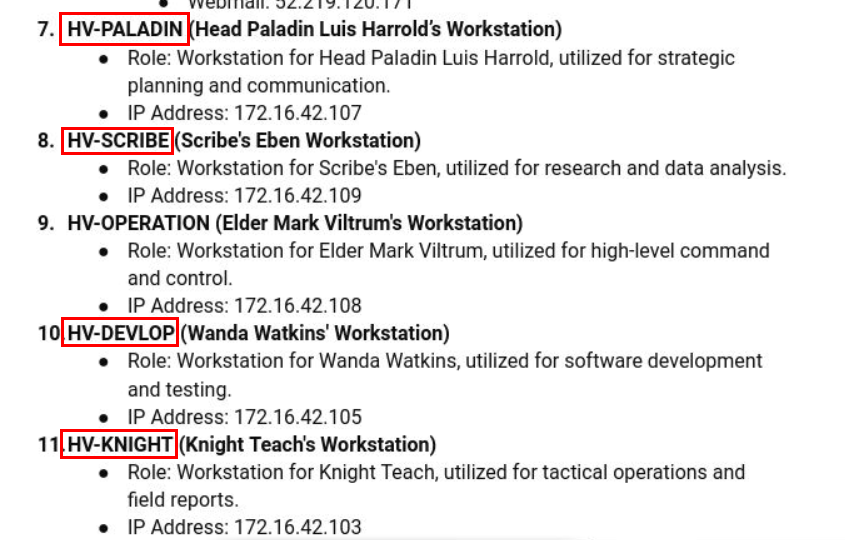 Go back to FSS Topology and match IP addresses to Machine name then we should have them in respective order to submit!
Go back to FSS Topology and match IP addresses to Machine name then we should have them in respective order to submit!
Answer
HV-PALADIN,HV-SCRIBE,HV-DEVLOP,HV-KNIGHT https://blueteamlabs.online/achievement/share/52929/209
https://blueteamlabs.online/achievement/share/52929/209
Summary
4 Hosts within FSS was infected with malware that beaconing to the same URL and it started from a malicious PDF file masquerade as png file.
IOCs
9484272e48f908e816a68f295a105d885b9d0ba52d8255d95c9bf237f71eae6b(SHA256 of malicious pdf)hxxp[://]hosting2022private[.]duckdns[.]org/eubp/example[.]ziphxxps[://]stcdanismanlik[.]com/Update/UpdatePDF[.]exehxxps[://]stcdanismanlik[.]com/Update/UpdatePDF[.]zip69[.]163[.]156[.]144hxxp[://]www[.]enclavenet[.]com/image